Common SSL Issues and How to Fix Them
You just installed an SSL certificate. The padlock shows up. Everything seems fine.
But then a warning appears.
“Not Secure” flashes in the browser. Your traffic drops. Your users hesitate.
Sound familiar?
Don’t worry.
You’re not alone. Even seasoned pros run into SSL problems.
a. Mixed Content Warnings and HTTP Resources
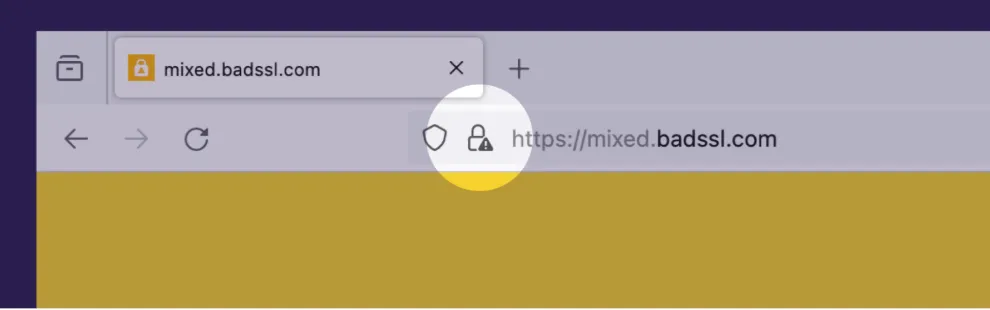
<img src=”http://example.com/logo.png”>
Even one line like that breaks the padlock.
Fix it by updating all resources to https://.
Use your browser console or a tool like Why No Padlock to find the culprits fast. Or check MDN’s Mixed Content guide.
Tip: Search your entire codebase or theme files for http:// and replace them. Or use plugins like Really Simple SSL if you’re on WordPress.
b. Expired Certificates and Auto-renew Failures
An expired SSL certificate is like showing up to a VIP event with an invalid ticket.
Your browser will flash a red warning, and users will panic-click away from your site. SEO bots won’t stick around either.
Many sites use free certificates from Let’s Encrypt but forget to automate the renewal.
The Fix: Set up auto-renewal using Certbot or your hosting control panel. And always monitor expiration dates (we recommend a calendar alert too just in case automation fails).
Additionally, use a service like Cronitor or StatusCake to alert you before your SSL expires.
c. Misconfigured Server Settings or Weak Cipher Suites
That is new! What are cipher suites?
Cipher suites are like secret menus 🤫. When your browser and a website connect securely, they quickly pick the exact recipes for encryption and security tools they’ll use for their private chat.
Learn more in the Cloudflare guide on cipher suites.
Ever scored your site on SSL Labs and got a B or C?
That’s usually because of weak protocols, outdated cipher suites, or missing security headers.
Some servers still allow TLS 1.0/1.1 (deprecated by IETF). Others don’t enforce HSTS, making them more vulnerable.
The Fix:
Edit your server config (nginx.conf or .htaccess) to disable weak protocols and enforce HSTS.
Always aim for an “A+” rating.
Security Tip:
Use only strong ciphers like TLS_AES_128_GCM_SHA256 and enforce TLS 1.3 for modern compatibility. Check official NIST TLS guidelines for reference.
d. Tools to Diagnose SSL Problems (SSL Labs, WhyNoPadlock, OpenSSL)
Let’s be real—you don’t need to be a server expert to spot SSL problems.
There are free tools that do the hard work for you.
Here are the ones I personally recommend:
🔍 SSL Labs
A deep-dive SSL test by Qualys. Tells you everything from cert validity to cipher strength.
URL: https://www.ssllabs.com/ssltest
🔍 Why No Padlock?
Pinpoints mixed content issues and insecure calls inside your webpage.
URL: https://www.whynopadlock.com
For techies: A command-line tool that lets you check certificates, renewals, and expiration.
Official docs: OpenSSL documentation
Command example:
openssl s_client -connect yourdomain.com:443








